Cyber Risk Management
Passwordless Authentication Architecture Based on a OneTime Code Approach
Welcome to the online security revolution! We’re here to explore a new authentication architecture – one that does away with passwords and replaces them with the efficient and secure power of a one-time code. Read on to discover how you can take advantage of this innovative technology and keep your data safe without compromising user experience. Lock in your data today – no passwords required!
Security is a primary concern for most organizations and the ability to authenticate users securely is essential. This paper presents a passwordless authentication architecture based on a one-time code approach using SMS or email-based single-use codes. This architecture combines multi-factor authentication (MFA) with a one-time code approach to provide an extra layer of security.
This paper provides an in-depth overview of the architecture, discussing the components involved and evaluating their security strengths and weaknesses. It also covers several considerations for implementing the architecture, such as how to generate codes, integration with existing systems, code expiration, and alternate methods of delivering codes. Finally, it provides real world application examples to show how this passwordless MFA can be put into action in real-world environments.
Benefits of Passwordless Authentication
Passwordless Authentication is a secure alternative to traditional username and password systems. This type of technology uses one-time code systems to validate users, thus providing better security, reducing the risk of fraud, identity theft and data breaches. Passwordless authentication has a range of benefits that make it an attractive option for organizations.
First, the use of one-time codes makes it impossible for a hacker to get access to confidential data as the code is valid for only one session and then expires. This strengthens security by eliminating the need to store passwords on databases that can be targetted by malicious actors. Additionally, as no credentials are stored in any location, brute force attacks targeting passwords become obsolete with this system.
Second, this type of authentication helps streamline user access processes and enables users to quickly and easily set up their accounts without having to remember complex passwords or multiple usernames or passwords. This simplification reduces the amount of time it takes for users to log in and increases user satisfaction with their experience when using the system. It also eliminates the need for IT staff or administrators, as no account creation activities or manual password resets are necessary, significantly increasing organizational efficiency.
Finally, this type of authentication also offers increased usability on mobile devices since no typing is required; users just have to open an authentication app and confirm access via their device’s biometric scanner or camera techniques such as facial recognition or fingerprint scanning. Having an easy-to-use platform helps reduce barriers often associated with mobile user experience which is an attractive benefit for many organizations that want secure yet accessible online platforms for their consumers and employees alike.
The One-Time Code Approach
The one-time code approach is a passwordless authentication architecture based on the principle of only allowing access after users have been verified through the receiving of a unique, time-sensitive code. This code is either sent via email or SMS to the user’s preferred communication method and must be entered for access to be granted. Such codes are only valid for a predetermined amount of time, most often 15 minutes but can range from 5 minutes to 24 hours depending on the organization’s security policies. The approach is favored in industries with strict security protocols due to its ability to verify users without additional knowledge or device information needed.
Advantages of this approach include ease-of-use, as no passwords need to be remembered, as well as an added layer of security in that these codes are usually tied to specific tasks or applications that require authentication. Limitations include a lack of authentication process flexibility and manually sending out codes for each individual authenticating user being time consuming and resource intensive when there are large amounts of users trying to authenticate at once.
Additionally it places reliance on maintaining network connections throughout the entire authenticating process which further reduces flexibility when there’s an unstable network present.
Advantages of the One-Time Code Approach
The one-time code approach has several advantages as a passwordless authentication architecture. First, it is secure: the code is difficult to intercept or guess, is tied to a specific application instance and cannot be reused. Second, it provides convenience for the user: the user’s contact information can be used to send a code that they can use instantly without having to wait for long authentication processes. Third, this approach allows for more granular control of users’ access rights since different applications and users can have different levels of access depending on their relationship with each other and the context of their operations. Finally, this also allows for increased scalability since only limited resources are needed in order to process multiple codes at once.
Challenges of the One-Time Code Approach
A One Time Code (OTC) is a unique, secure password or code that can only be used once. It’s generated for a specific purpose and can’t be reused afterwards.
The One-time Code (OTC) approach offers a secure and convenient authentication method based on time-limited code or envelopes exchanged between users and the authentication server. While this authentication architecture makes it easy for administrators to deploy and manage such systems, there are several challenges that should be considered:
- Scalability – In order to meet the needs of a large user base, it is important that the OTC approach is able to easily scale with additional users. Since OTC messages are typically sent through email or SMS channels, additional bandwidth may be required for increased user numbers which can create scalability issues.
- Authentication delay – OTC messages can sometimes be slow to arrive leading to potential delays in user authentication. This can lead to user frustration and decreased security as hackers begin guessing passwords faster than codes can be sent out.
- Reliability – As stated previously, OTC messages are typically sent via email or SMS channels which means there is always the possibility of delivery failures due to network latency, technological issues or even bad addresses/phone numbers being used for messaging purposes. It is important that there are redundancies in place in order for an authentication process based on one time codes remain reliable and secure at all times.
- Phishing attacks – Since code messages usually contain information related to sensitive accounts such as bank data, they can be easily intercepted by malicious actors looking to exploit this feature of the OTC approach by initiating phishing attacks against unsuspecting victims.
- Implementing the One-Time Code Approach – For organizations looking to implement a passwordless authentication architecture based on the one-time code approach, there are several steps that need to be taken. First, a user needs to initiate the authentication. This might be through a browser window or an app, or even an SMS message containing a one-time code sent directly to the user’s device. The user then has to provide the one-time code along with any other factors necessary for authentication (e.g., biometrics). Once these steps have been completed, the organization will check if the given code is valid and if all of the other factors match what’s stored in their system for that particular user. If everything is valid and correct, then access will be granted; otherwise, access will be denied. Additionally, organizations can look into implementing two-factor authentication approaches where more than one factor is required for access (for example, entering in both a username and password). Implementing this approach can help add an extra layer of security.
- Security Considerations – While passwordless authentication has the potential to help improve user experience without introducing additional security risks, some issues should still be taken into consideration and dealt with appropriately.
When designing a system for passwordless authentication, it’s important to understand that any control must take into account the security and privacy of the users. Security considerations include the following:
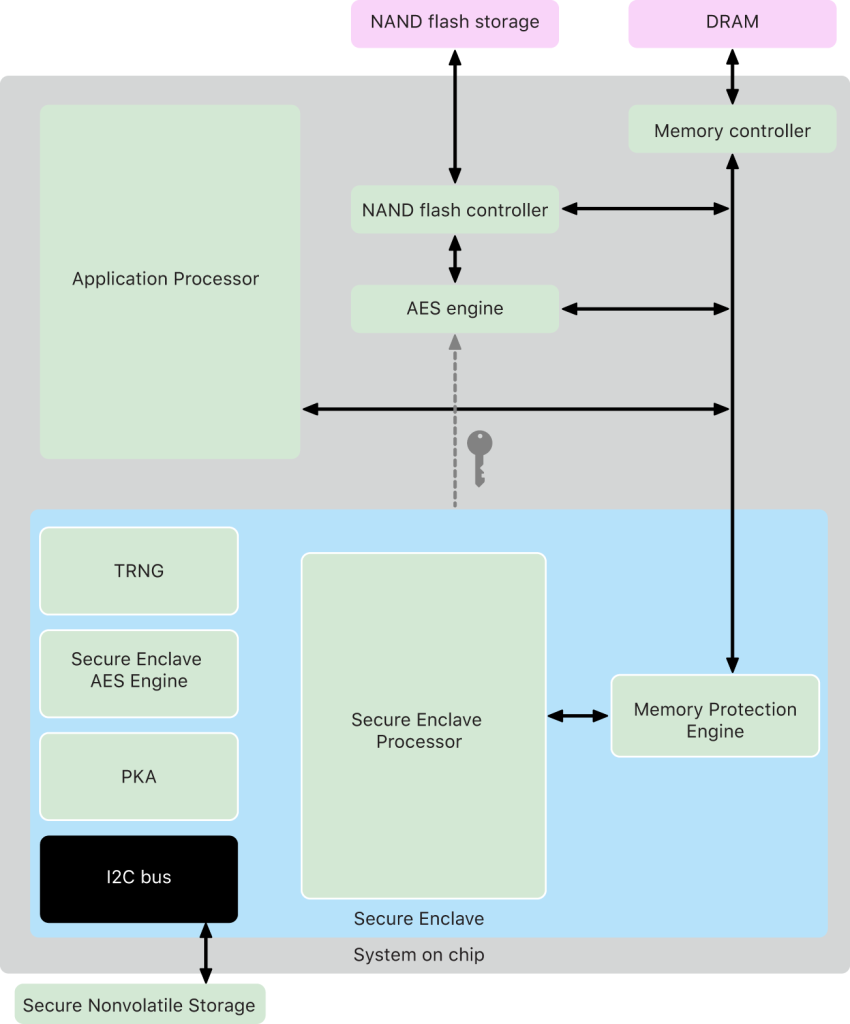
–Encryption: Authentication tokens should always be encrypted with a secure key or protocol in order to protect them from unauthorized access.
–Authenticode verification: Any codes sent for login should be authenticated before being accepted by the system in order to prevent attackers from trying multiple combinations until they find one that works.
–Mobile app protection: Native mobile apps need to be protected against reverse engineering in order to prevent malicious actors from gaining access to the authentication tokens used by users.
–Data integrity: All communication should be secured using protocols like TLS or VPNs in order to ensure data confidentiality and integrity between the service provider and its customers.
–Timeouts: All authentication attempts should have an associated timeout value, which would prevent attackers from attempting brute force attacks with unlimited guesses. If an attacker is unable to guess after a certain number of attempts, they must start again from scratch.
Conclusion
This paper has proposed a solution based on One Time Code (OTC) to authenticate users without passwords. The proposed approach simplifies the user experience of the authentication process and so makes it easier for them to authenticate through the app. An important benefit of this approach is that users do not need to remember passwords, making up for one of the main issues in modern authentication methods that rely on password as an authentication measure.
Moreover, as passwords are replaced with OTCs, brute-force attacks are also avoided and security is increased as a result. In addition, OTCs are employed in conjunction with established identity providers to enhance user security further by cross-checking with user specific criteria before the actual logon process takes place.
The implementation of this approach introduces several challenges such as requiring implementation of mechanisms like Push Notifications and expiration checks while avoiding scenarios commonly witnessed in other attempts such as Heimdal’s Hack and man-in-the-middle attacks .
Developers must consider integration points when architecting their own OneTime authentication system, such as being able to track requests from different sources using a Device ID or any other unique identifier associated with each request directed towards OTP Server for verifying a user’s identity.
In conclusion, passwordless authentication does provide a secure and easy way for end users to authenticate, however due care must be taken during the architecture process.