Cyber Risk Management
Are Passwords Obsolete?

Increasingly, we see an organizational move away from the use of passwords, at least in the traditional sense. Companies are working to meet the changing demands of more remote and hybrid work. They need to ensure that users can access resources securely but remain productive.
A lot of this comes from using features like single sign-on and multi-factor authentication.
Both are part of a Zero Trust architecture, and along with these concepts, many are questioning whether or not passwords will become altogether obsolete. Below, we explore the topic.
Passwords are Still Alive… for Now
The discussion about the death of the password started nearly 20 years ago at the RSA Security Conference. In 2004, passwords were described as not being able to meet the challenge of securing critical resources. At that time, it was said their extinction was inevitable.
Here we are, all this time later, and passwords are still with us, but their death is still being discussed.
Even though we have made tremendous advances in so many technology areas, we still rely on passwords for security.
Last year, hackers were able to breach Colonial Pipeline Company with one single compromised password. After shutting down the largest fuel pipeline in the country, the hackers were able to walk away with $4.4 million.
That left many once again questioning why passwords are still so often used as the only authentication factor.
While passwords are alive, largely due to convenience, their ability to be your company’s sole source of protection is very much dead.
That brings the world to the multi-factor authentication (MFA) era.
Why Are Passwords Alone So Problematic?
Employees often use weak passwords or reuse them.
Recent research finds that the word itself, password, is still being used as the most common password in all industries. Other passwords that are commonly used include Hello123 and sunshine.
Around 20% of passwords researchers recently uncovered were either the exact company name or a small variation.
In some industries, employees have their particular types of a weak passwords. For example, in the financial sector research, profit was a common one, and in energy, it was snowman.
We can think back to the SolarWinds hack, which was triggered by someone using the password solarwinds123 to protect a secure server.
Company officials say the weak password wasn’t the reason for the hack, but they were warned of a weak password by a security expert, and then took two years to change it.
In 2019, according to Verizon’s Data Breach Investigations Report, compromised credentials were the reason for 80% of all data breaches.
Phishing scams are the most common type of cyberattack directed at passwords. In a phishing scam, employees give their credentials in response to fake emails or spoofed websites.
A cybercriminal can also use automated tools like a brute force to guess passwords.
Cyber attackers can steal credentials through malware or from database dumps of stolen passwords or try to crack coded versions of a password that an organization stores in their system.
It’s very difficult for anyone to remember a random, complex password. The average online user also has at least dozens of accounts online, requiring a password. There’s a very high likelihood that they’ll use the same or at least a very similar password across sites, and often both business and personal accounts.
How Can Multi-Factor Authentication Help?
We can talk about passwords being dead or obsolete all we want, but the reality is the conversation is decades in the making, and we’re still using them.
Rather than planning for passwords to be entirely obsolete, it’s better to consider other security measures—namely, multi-factor authentication or MFA.
MFA adds another layer of authentication on top of a password when someone goes through the login process, significantly improving security.
With the enabling of MFA, a hacker can’t get into a system with just a stolen password. They’ll also need another factor, like a security code that’s randomly generated and sent to your smartphone.
The vast majority of hacking occurs remotely, so MFA can safeguard against hacking almost entirely.
According to the Center for Internet Security, MFA is the recommended first-line approach for authentication. Second, to that recommendation is the use of password policies.
Password Replacements
There are password replacement options, although they might not be the right fit for every organization right now.
- Some organizations are using passphrases rather than passwords. A passphrase is a longer mix of words, and it can add curveballs to the typical password. While passphrases are one option, you have to remember they’re still going to be incredibly weak if they’re being reused.
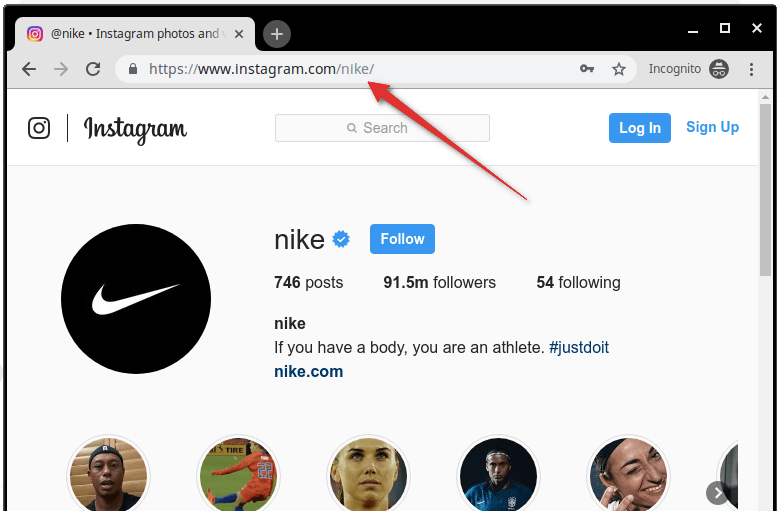
- Organizations are increasingly adopting single sign-on. With single sign-on, the end-user experience is easier because the users can rely on one username and password to access various programs and services. However, the problem here comes in when a cybercriminal gets access to all systems if they compromise the SSO itself.
- We talked about multi-factor authentication above, and if you talk to cybersecurity professionals, they’ll tell you how valuable it is. We briefly went into how it works, but MFA lets your users access data by providing two of three possible things. The first is something you know, which can be a password but also a PIN. Then, the second can be something you have. This is also called an ownership factor. It could be a physical item, like a smartphone. The third is something you are, also known as biometric factors. Biometric factors can include voice recognition, fingerprints, or retina scans.
- Passwordless authentication systems rely on two elements of MFA—something you have and something you are. There’s no password that your users have to remember or that can potentially be stolen. Many of these passwordless systems will include some public-key cryptography that will generate a unique key to log in with.
- PINS aren’t the same as passwords, and they can be tied to a specific physical device, so it becomes the “something you have” MFA factor.
Finally, advanced threat detection and endpoint detection tools can also provide a way to stop a hacker, even if they’ve managed to get a username and password.
-

 Cyber Risk Management4 days ago
Cyber Risk Management4 days agoHow Much Does a Hosting Server Cost Per User for an App?
-

 Outsourcing Development4 days ago
Outsourcing Development4 days agoAll you need to know about Offshore Staff Augmentation
-

 Software Development4 days ago
Software Development4 days agoThings to consider before starting a Retail Software Development
-

 Grow Your Business4 days ago
Grow Your Business4 days agoThe Average Size of Home Office: A Perfect Workspace
-
Solution Review4 days ago
Top 10 Best Fake ID Websites [OnlyFake?]
-
Business Imprint4 days ago
How Gaming Technologies are Transforming the Entertainment Industry
-

 Gaming Technologies2 days ago
Gaming Technologies2 days agoHow to Set Up Text-to-Speech for Channel Points on Twitch