Cyber Risk Management
Ways to Prevent SQL Injection Attacks

SQL injection is a common cybersecurity issue used by attackers as an entry point to your database. It can be a precursor of many other attacks like credential stuffing, account takeovers, and other forms of fraud. Therefore, it is essential to understand how to protect the application’s database to avoid heavy losses from SQL injections. In this post, we will discuss various ways that you can use to prevent SQL injection attacks.
Ways to prevent SQL injection attacks
Among the most dangerous threats to web applications today are SQL injection attacks. All is not lost to a network or database admin because there are various ways to prevent them from ever happening or minimize their occurrence frequency.
As we will see below, you can take various steps to reduce the risk of exposure to SQL injection attacks.
Regular auditing and penetration testing
It is becoming increasingly necessary to perform regular application, database, and network audits nowadays. With regulations like GDPR, a company does not have the luxury of relaxing on matters of database security. In addition, auditing the database logs for suspicious activities, privilege escalation, and variable binding terms are necessary practices.
As crucial auditing, the system for malicious behavior is, it is equally essential to perform penetration testing of your database to gauge the readiness of your response mechanisms to potential attacks that include SQL injection. Penetration testing companies can find threats like cross-site scripting, unpatched vulnerabilities, retired software, insecure password, and various forms of SQL injection.
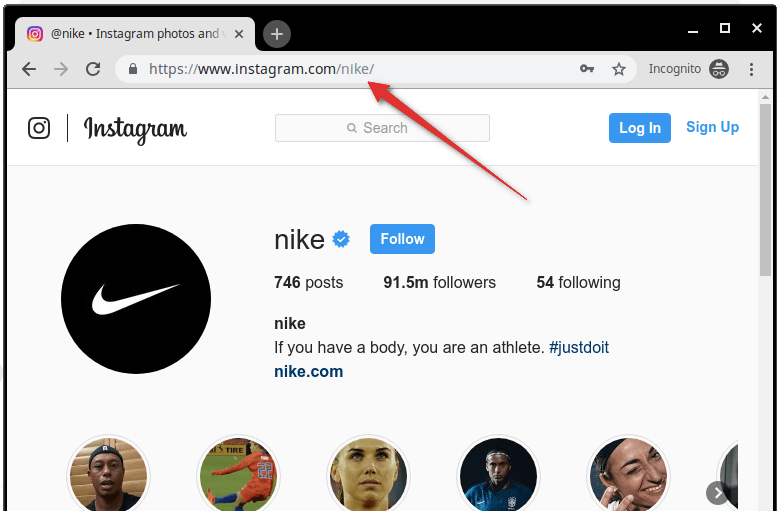
User Input Validation
Validating the user inputs is a common step to preventing SQL injection attacks. You have first to identify the essential SQL statements and make a whitelist containing all valid SQL statements. This leaves out the invalidated statements. We refer to this process as query redesign or input validation.
Ensure you configure inputs for user data by context. For instance, you can filter email addresses to ensure that only strings that contain specific characters such as “@” are allowed. In a similar fashion. Ensure that you filter the social security and phone numbers using regular expressions to allow a specific format and number of digits in each of them.
Sanitization of data through special character limitations
You can safeguard your database against SQL injection attacks through adequate sanitization of user data. SQL injection attackers use specific character sequences that are unique to exploit a database. Therefore, sanitizing your data not to allow concatenation of strings is a critical measure.
You can achieve this by configuring the inputs from a user to a function. It ensures that an attacker does not pass characters like quotes in an SQL query as they might be dangerous. Various administrators use prepared statements to avoid unauthenticated queries.
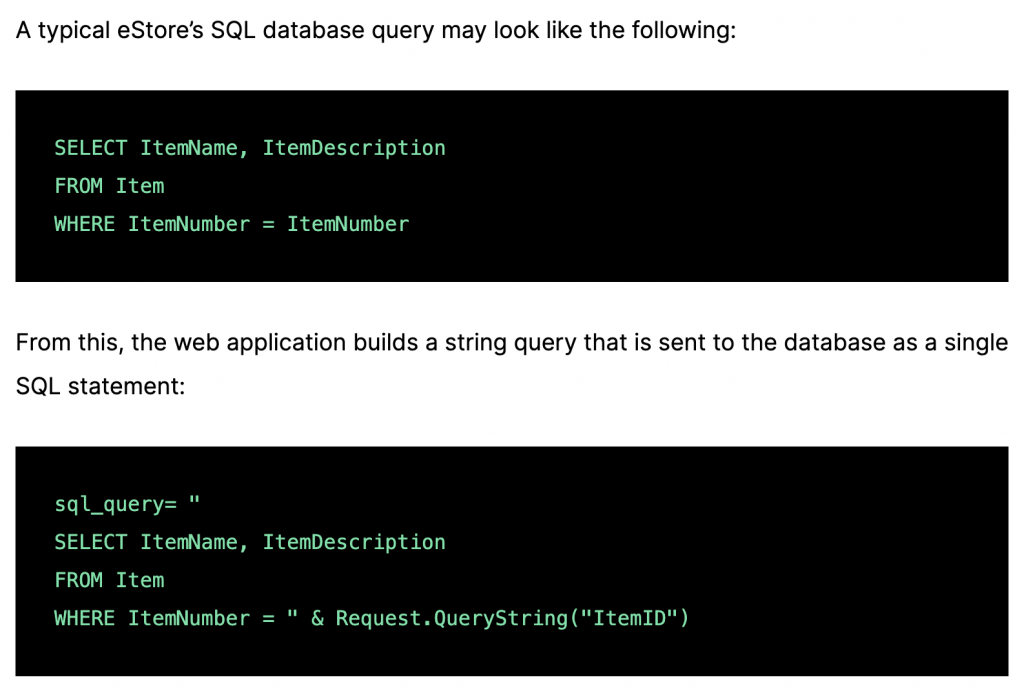
Parameterization and enforcing prepared statements.
Input validation and data sanitization do not fix all SQL injection-related issues. Therefore, organizations must use prepared statements containing queries that are parameterized to write database queries. We also call this variable binding. Distinguishing user input and code is made easy to define the SQL code used in a query or a parameter.
Although dynamic SQL as a programming method allows more flexibility in developing an application, it has the drawback of allowing SQL injection vulnerabilities as instructions. In addition, sticking to the standard SQL means malicious SQL inputs will be treated as data but not as a potential command.
Enforcing stored procedures in the database
Stored procedures use variable binding like parameterization. Unlike mitigating SQL injections using prepared statements, when you implement stored procedures, they are resident to the database and are only called from an application. If you use dynamic SQL generation, they minimize the effectiveness of stored procedures. According to OWASP (The Open Web Application Security Project®), only one parameterized approach is required, but neither is enough to guarantee optimal security.
Increasing the capability of the virtual and physical firewalls
To help fight malicious SQL queries, we recommend using software or appliance-based web application firewalls. Both NFGW and FWAAS firewall offerings are easy to configure and have a comprehensive set of rules. If a software security patch is yet to be released, you can find WAFs to be useful. One popular firewall is ModSecurity. It is available in Microsoft IIS, Apache, and Nginx servers. It has ever-developing and sophisticated rules to help filter potentially dangerous requests from the web. Its defenses for SQL injection can catch many attempts to sneak in malicious SQL queries from the web.
Reducing the attack surface
An attack surface is an array of vulnerabilities that an attacker can use as an entry point. Therefore, in the SQL injection context, it means that you do away with any functionalities in the database that you do not require or ensure further safety.
A good example is the xp_cmdshell extended storing procedure for the Microsoft SQL Server. It can spawn a command shell and pass a string for execution in windows. Since the process started by the xp_cmdshell has similar security privileges as the SQL Server service account, severe damage from the attacker can befall the database.
Encryption
One rule should always reign when dealing with matters on the internet. No connected application is secure. Therefore, ensure that you hash and encrypt your connection strings and confidential data. There are many encryptions and hashing tools that are cheap, easily accessible, or even open source. Today we must universally adopt encryption as a data protection mechanism. It is for a good reason. Without encrypting your data using appropriate hashing and encryption policies, when it falls in the hands of a malicious actor, all the data is in plain sight. There are various hashing mechanisms like SHA, LANNAN, and NTLM. Encryption algorithms in the market today are bcrypt, DES, RSA, TripleDES, among many others. According to Microsoft, through encryption, we transform the problem of protecting the data protecting cryptographic keys.
Monitoring the SQL statements continuously
Third-party vendors and organizations should ensure continuous monitoring of all SQL statements within an application or database-connected applications. They should also document the prepared statements, database accounts, and stored procedures. It is easier to identify SQL statements that are rogue and various vulnerabilities when you scrutinize the functioning of the SQL statements. Therefore, a database admin can disable or delete unnecessary accounts, the stored procedure, and prepared statements.
There are monitoring tools that use technologies like behavioral analysis and machine learning. They include tools like SIEM and PAM and are an excellent addition to an organization’s network security.
Take away about prevent SQL injection
It is essential to conduct regular penetration testing to evaluate how you have implemented measures to prevent SQL injection attack responses. Through this option, you can stay ahead of the attacker and prevent lawsuits and hefty fines from coming your way. Besides the above measures, you can implement other safeguards like limiting access, denying extended URLs from your application, not divulging error messages, among many others.
-

 Cyber Risk Management3 days ago
Cyber Risk Management3 days agoHow Much Does a Hosting Server Cost Per User for an App?
-

 Outsourcing Development3 days ago
Outsourcing Development3 days agoAll you need to know about Offshore Staff Augmentation
-

 Software Development3 days ago
Software Development3 days agoThings to consider before starting a Retail Software Development
-

 Grow Your Business3 days ago
Grow Your Business3 days agoThe Average Size of Home Office: A Perfect Workspace
-
Solution Review3 days ago
Top 10 Best Fake ID Websites [OnlyFake?]
-
Business Imprint3 days ago
How Gaming Technologies are Transforming the Entertainment Industry
-

 Gaming Technologies1 day ago
Gaming Technologies1 day agoHow to Set Up Text-to-Speech for Channel Points on Twitch